The fact is that phishing messages are all over the place. It doesn’t matter if you are a large corporation or a small business with only a dozen employees; the threat of phishing attacks is real and should be prepared for. Thankfully, one of the easiest ways to avoid phishing messages is as easy as moving your mouse. We are, of course, talking about hovering over links.
Indevtech Blog
Multifunctional printers can be indispensable business tools. However, they also pose significant security risks, potentially serving as entry points for cybercriminals seeking to exploit vulnerabilities and pilfer sensitive data and resources. Safeguarding your organization against these threats is paramount. This blog post will explore key measures to fortify your networks against printer-based vulnerabilities.
You or one of your employees may need to work while on the road for many reasons. Unfortunately, this can be dangerous if you aren’t careful. We wanted to take a few minutes to (hopefully) review some security best practices your entire team should follow should they ever find themselves working as they travel.
It seems like with every day that passes, there is a new sinister cyberthreat to worry about, and it’s crucial that businesses learn as much as possible about how to keep themselves safe as they can. There is simply too much at stake not to. That said, there are broad categories that most threats will fall under. Today, we’re going to explore them.
Network security is complicated, and as such, you need to have considerable knowledge of it to ensure that your business is as secure as possible against the plethora of threats out there. Thankfully, you don’t have to do it alone. We want to give you some insight into the dos and don’ts of network security.
Opening a new location is an exciting event for any business, but it's not without a litany of difficult decisions to make. One thing is certain, challenges always emerge. One thing you can do is plan your technology needs strategically to avoid headaches in that arena. Today, we take a look at how to best get your new location outfitted with the technology it needs to succeed.
Business Intelligence (BI) is a platform that uses the data that your business creates to help you make advanced business decisions. Starting to use data for business intelligence involves several key steps to effectively gather the data you want to sort through and successfully analyze it in a way that can allow you to understand your business better.
As remote access has enabled more and more people to work from home, a business’ security has become harder to reinforce. After all, while you can control the solutions you have protecting your business, you don’t have much control over the solutions that your employees have at home. Here, we’ve provided some of the best practices that you should reinforce when your team is working remotely.
Phishing attacks are the most common attack vector used by hackers, and while it helps to know what a phishing attack looks like, it’s also good to know what they don’t look like. The latest example of a phishing attack takes this to an extreme, utilizing blank messages to confuse recipients in a creative take on phishing attacks.
Wouldn’t it be great if your business didn’t have to worry about technology problems? Well, with the right amount of attention and care invested, your business can minimize technology issues and optimize your infrastructure for proactive technology management rather than reactive. Let’s go over some of the most important practices.
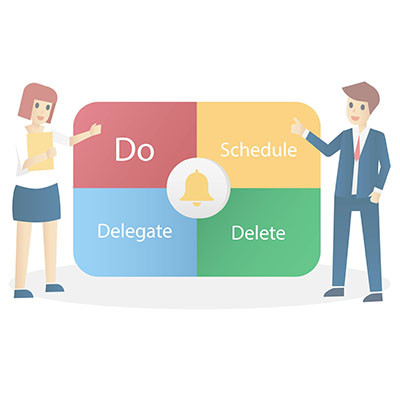
If you have a to-do list a mile long, then you’ll need to develop a system to place priority on what truly matters and what could be put off until a bit later. Thankfully, you don’t have to develop a system from scratch, as one of the more interesting methods for tackling your to-do list has already been developed and inspired by a 1950s speech: the Eisenhower Matrix.
As your business grows and shifts, managing your technology can become increasingly complicated. It can get to the point where properly taking care of your IT and supporting your users is a full time job. If you are just calling a computer person to come and fix problems when you bump into them, then you might have potential consequences to deal with later that could cost your organization a lot of time and money.
Productivity will always be the primary goal for businesses, right alongside profits, although one thing does in fact lead to another in this case. To ensure your company runs efficiently, you need to understand just how productivity works and its relationship with what you put into your business. We’ll be using the next couple of weeks to take a closer look at the relationship between your business and its productivity.
First, let’s look at what productivity is, in its simplest and purest form.
With more people depending on technology, it stands to reason that there are more scams out there than ever before. The individuals (and groups) responsible will look for and exploit any vulnerability to attack your employees in order to get at your business’ critical data. Let’s take a look at a couple of tips that you can use to keep your passwords strong and your password-protected accounts secure.