In recent years, the Internet of Things (IoT) has emerged as a game-changer across various industries. One way that businesses can utilize these technologies is to understand how their businesses use their utilities as well as automate the control of some of them to cut costs and utilize these resources more efficiently. Let’s look at how businesses are using IoT tools to stabilize utility costs.
Indevtech Blog
In business, organizations that are able to automate processes have a leg up on organizations that rely on humans to do everything. Not only does it cost a lot less to run a business that has automated processes, it also helps improve organizational focus and efficiency by streamlining processes and removing the moving parts that can sometimes hinder operational progress. That’s not to say that there aren’t some places that a business can greatly benefit from a human touch. Let’s take a look at both sides of the argument.
By now you’ve probably heard the term Internet of Things (IoT). You may not completely understand what it is, but you know it has something to do with all those “smart” devices that you see popping up everywhere. Today, we’d thought we’d get into what types of things are on the IoT and how they can have an impact on your business.
The difference between productivity and innovation is not always clear-cut, but the biggest one is that higher productivity naturally creates innovation… assuming it is supported by the right tools and mindset. How can technology help your business be more creative and innovative in the way it goes about its day-to-day operations?
Automation as a concept is on the rise, and so too is its practice. Even before COVID-19 created considerable problems for several businesses, it was in use, and there is no reason for it to fall out of fashion now. There are plenty of ways your organization can implement automation to improve operations moving forward.
Most companies have some sort of human resources department. Some are bigger than others. Some are more effective than others. Typically, the HR department deals with a lot of the stuff that no one else likes to. Today, software is being created using artificial intelligence that will be able to complete many of these tasks. Let’s take a look at how automation is affecting the modern human resources department.
Most industries utilize automation to at least some degree. With plenty of benefits that can be taken advantage of, businesses need to remember that they still must be careful about implementing these systems, as failing to do so could cause downtime and negatively impact productivity. Here are some of the major benefits and detriments that your organizations should consider when examining automation.
Information technology, in many ways, is a necessary evil. Sure, modern businesses more or less require it to remain competitive, but it also opens up your business to a multitude of threats. Maintaining your security is made much easier with automated monitoring tools. Today, we’ll discuss how to use these tools to protect your business.
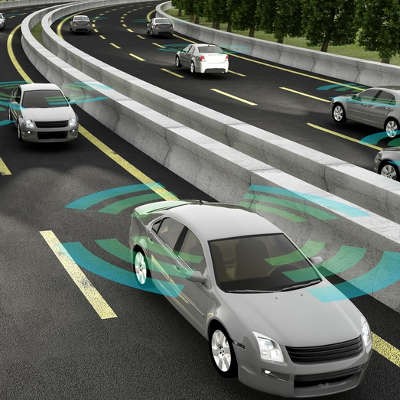
By now you’ve heard of self-driving cars insofar that you understand that there are engineers from all over the United States and abroad working with AI to develop systems that can create safer traffic conditions and cut down on emissions with efficiency. But what you may not know is that there are many drivers concerned at the development and deployment of these autonomous systems.
 Eliminating unnecessary costs is a natural part of doing business. By “trimming the fat,” so to speak, organizations can optimize operations and profits. Automation technology is instrumental to this plight, but as these systems grow more advanced and capable, even professional employees are finding themselves at risk of losing their jobs to cheaper, more efficient automated systems.
Eliminating unnecessary costs is a natural part of doing business. By “trimming the fat,” so to speak, organizations can optimize operations and profits. Automation technology is instrumental to this plight, but as these systems grow more advanced and capable, even professional employees are finding themselves at risk of losing their jobs to cheaper, more efficient automated systems.
 Artificial intelligence might be quite a ways off, but despite this, the push continues to make driverless cars a regular occurrence on the roads. Just look at how Google has its driverless cars rolling across testing grounds in Mountain View, California, and if they have their way, we might see a lot more of these vehicles hitting the roads in the near future.
Artificial intelligence might be quite a ways off, but despite this, the push continues to make driverless cars a regular occurrence on the roads. Just look at how Google has its driverless cars rolling across testing grounds in Mountain View, California, and if they have their way, we might see a lot more of these vehicles hitting the roads in the near future.
 The point of living in a world where technology takes over everything is that it’s supposed to make life easier. Although, keep in mind that imperfect humans are responsible for creating these technologies. Therefore, technology is flawed, maybe even to the point of putting people in harm’s way. This fundamental truth makes for an uneasy trust between man and machine.
The point of living in a world where technology takes over everything is that it’s supposed to make life easier. Although, keep in mind that imperfect humans are responsible for creating these technologies. Therefore, technology is flawed, maybe even to the point of putting people in harm’s way. This fundamental truth makes for an uneasy trust between man and machine.
 Some people talk to their computers, but not like they would speak to another human being. We coax it into doing it what we want, or we curse it out when it doesn’t. A day may come when artificial intelligence has progressed so far that we won’t be able to distinguish a computerized conversation from a normal one; but it is not this day. Until that glorious day comes, we’ll have to settle for these two methods to interact verbally with your PC.
Some people talk to their computers, but not like they would speak to another human being. We coax it into doing it what we want, or we curse it out when it doesn’t. A day may come when artificial intelligence has progressed so far that we won’t be able to distinguish a computerized conversation from a normal one; but it is not this day. Until that glorious day comes, we’ll have to settle for these two methods to interact verbally with your PC.